This post will walk you through the simple steps to turn off (and on) the Print Spooler service within the Windows operating system. You can apply the steps to any service, for that matter.
Among other things, this skill allows you to get more control of your Windows computer. And for right now, it’ll keep you safe from the newly-discovered and severe vulnerability in Windows.
What are “services,” and what’s up with Print Spooler?
Microsoft uses the term “service” to call a core component of its Windows operating system. So services are software that runs together with the OS itself, without the intervention of the user.
(Other operating systems have similar components. Unix (Linux) and macOS often refer to them as daemons).
There are also third-party services not made by Microsoft but are essential for certain hardware components to work.
Most services run automatically the moment Windows fully boots up or when a user logs in. Other run on-demand when the hardware or other services need it. A user (with the administrator privilege) can force a service to stop, start, or disable it completely.
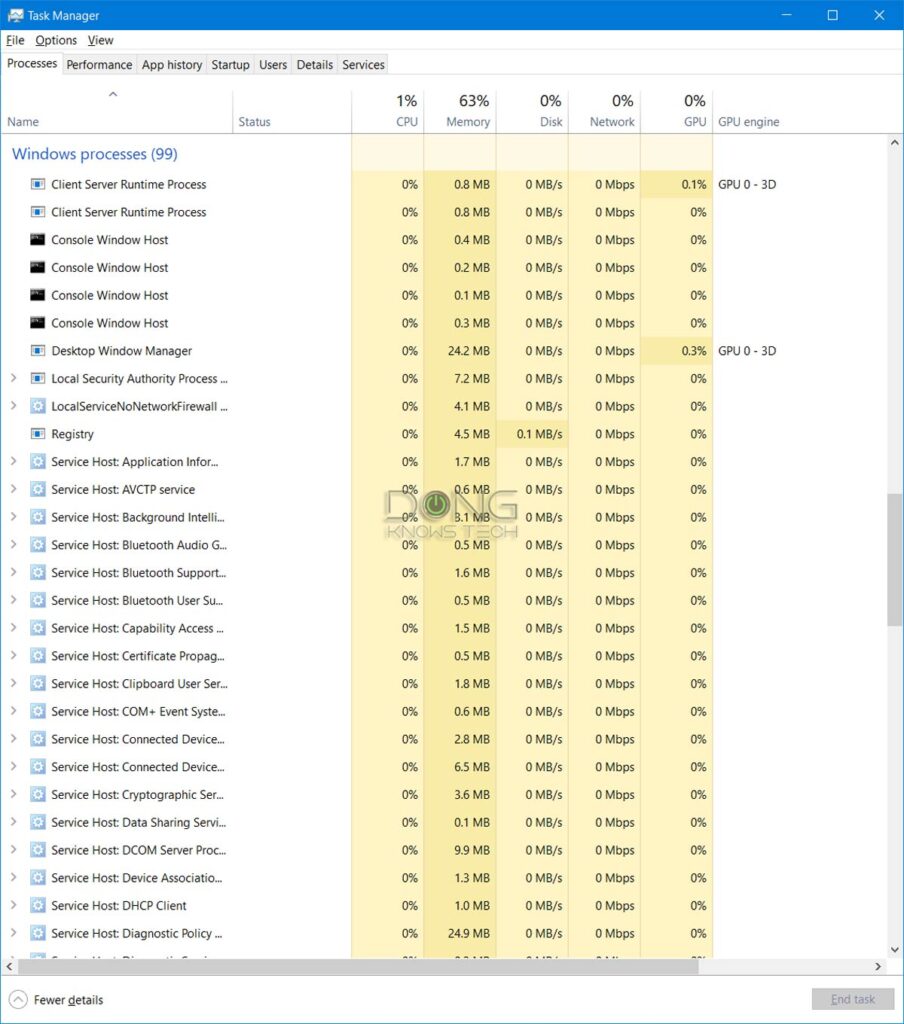
On a computer, you can view the list of running services by opening the Task Manager. (Right-click on the Start button, then choose Task Manager on the menu.) They are listed under Background/Windows processes.
The Print Spooler service’s latest security vulnerability
The Spooler is one of the original and most essential services of the Windows OS. It has largely remained the same in the past few decades and is available in virtually all in-use versions of Windows.
As of July 1st, 2021, Microsoft has provided a security advisory about this service. Specifically, when running, it could allow hackers to run malicious code on your computer remotely. It’s a kind of vulnerability as bad as can be, especially considering the threats of ransomware.
To put this in perspective, Print Spooler is an important service—without it running, a computer cannot print at all. Yet, Microsoft’s recommended workaround, for now, is to disable it.
The company’s included instruction to do that was a bit had for novice users to follow. That’s partly why I wrote this post.
Update: On July 7, 2021, Microsoft released a security patch via Windows Update to address the issue.
Step to manage Print Spooler or any service in Windows
Below are the steps you can take to manage any service in Windows 10—they can apply all versions of Windows, however.
Generally, you don’t want to mess with Windows’ services, but its’ OK to do so with the Print Spooler—at worst, you can no longer print, and that’s the only way to stay safe until the vulnerability is patched.
1. Call up the Services tool

To manage its services, Windows has a built-in app called, well, “Services.” You can search for it on the Start Menu then click (or tap) on it. The Services window will appear.
2. Open the service in question

On the Services app’s window, you’ll note a long list of services. Click on the Name column to sort them alphabetically. Now locate the service in question, which is the Print Spooler in this case, and double click on it.
3. Manage the service

Here you can manage the service’s Startup type:
- Automatic (Delay Start): The service will run once the computer turns on with a bit of delay.
- Automatic: The service will run immediately when the computer starts.
- Manually: An user needs to turn run it manually.
- Disabled: The service will not run at all.
On top of that, the user can also Stop a service (if it’s running) or Start it (if it’s not.)
So for this, you can pick the Startup type of the Print Spooler service to be either Manual or Disabled. Then Stop it.
When you want to (temporarily) reverse the process. You can repeat until step #3 and Start the service, and then change the Startup type accordingly.
And that’s it! Again, you can do that with any of the services. Just make sure you have a good reason to do so.

Final thoughts
As you’re reading this, chances are the Print Spooler service vulnerability is being exploited, and there’s no patch for it yet.
While your chance of getting affected by this vulnerability is relatively low, it’s a good idea to disable this service until a patch is available—hopefully soon. Or you can also run it manually when you want to print, then turn it off.
Alternatively, you can turn the computer off when you’re not using it or disconnect your print server machine—more applicable to a business environment—from the Internet.



Once again you cut through so much chaff and tech-speak to lay out clearly in terms ordinary mortals can understand as well as act on.
Thank you, Dong Ngo.
Sure, Ian. Glad you found this helpful. 🙂
In reading more about this on the web, is this one really a danger for personal machines (not in an active domain controller environment) behind a typical home NATed router? It seems like the main danger is that a non-priv account in an ADC environment can use this bug to get elevated privs on another machine in the same ADC environment. What is the danger to a typical personal machine in a non-ADC home environment? Thanks.
It’s dangerous for everyone using Windows, Randall. But the chance of being affected is *low*. The issue is there’s no patch yet and the method to exploit is public knowledge. I think MS was caught a bit off-guard on this one.